REDUCE END USER ATTACKS WITH
Email Phishing Simulation & Reporting
End to End managed with certified security experts.
No software or hardware to install at client premises.
Real world scenario tests with backed with our threat intelligence.
Managed Service
End to End Managed
Dedicated manager to drive campaigns with compliance reporting.
SaaS Model
No software to install
No hardware or software to buy or maintain.
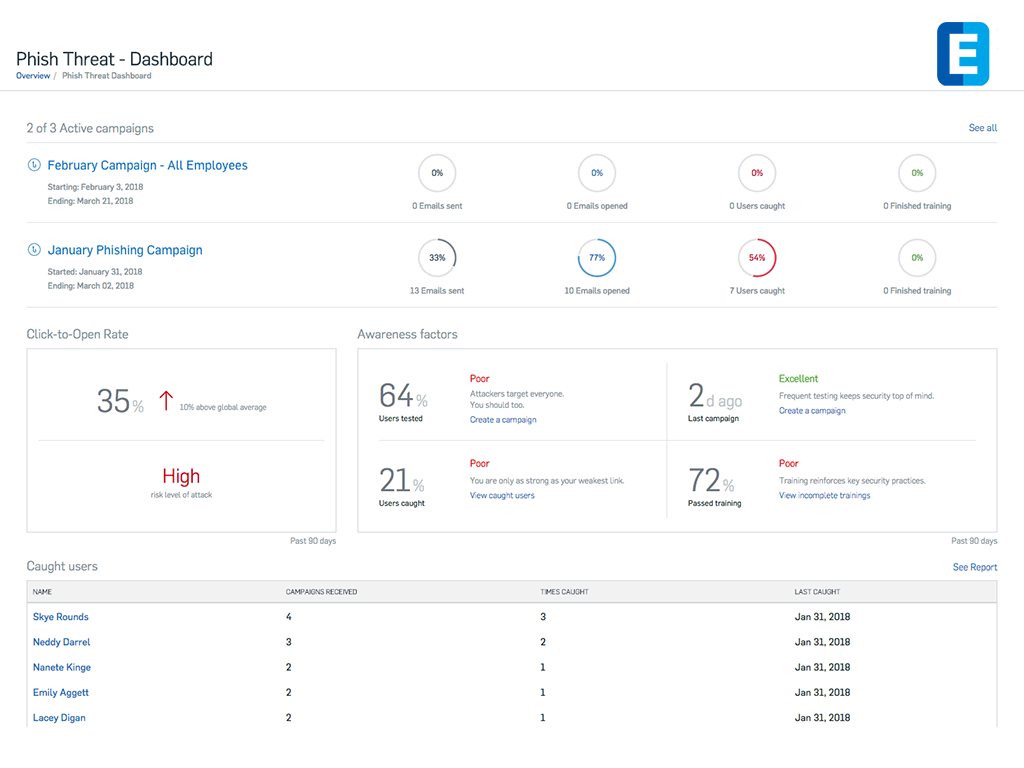
Reporting
Meet security and compliance
Get the data you need to identify security weaknesses.
User Training
Phishing and Social Engineering
Use our training platform to reduce your employees' risk from cyber attacks.
E Mail Phishing Simulation
Custom campaigns with links and Fake log-in pages.
Custom spoofed sender based on the scenario.
Identify complete user profile with interactions.
Our Approach
Template creation
Create a custom phishing or malware simulation to address specific needs.
Launch
Use custom sender id based on requirement and select channel via Mail, SMS.
Measure
Capture user activity like link clicks, file downloads, form submits, etc. in real time
Analyze
comprehensive report that includes Campaign results, trend of vulnerable users and reporters.
SMS Phishing Simulation
Create simulation with links and Fake log-in pages.
Custom sender id support for effective campaigns.
Every user interaction and user profile fully recorded for reporting.

Why Us?
Globally available
Largest technology practice with a network of practitioners in more than 30 countries.
Threat Intelligence
Backed with our Counter Threat Unit to conduct simulations based on real-world risks.

Recognised leader
More than a decade of experience in IT advisory, consulting and assessment.
Expertise
Dedicated practice of over 300 security experts, analysts and researchers.
Cost effective. Flexible plans.
Comprehensive reporting.
| Pricing Tier/ Product |
Phishing Simulation/ Per user |
Phishing Simulation with Training/ Per user |
| Up to 100 | $10 | $35 |
| 101-250 | $8 | $28 |
| 251-500 | $7 | $22 |
| 501-1000 | $5 | $18 |
| 1000+ | Get a Quote | Get a Quote |
Contact the sales representative in your geographic region for current promotions or upgrade discounts.

